It is no secret that security is an absolutely crucial part of computing in the modern era. Data can very fairly be called the most valuable currency today, which means it needs to be protected. One way to do this is through the use of encryption keys. In this Tech Term, we’ll go over how these keys can protect your data, and how they do so.
The Connection, Inc Blog
The European Union’s General Data Protection Regulation (GDPR) has gone into effect, and with this new law comes a lot of information your organization needs to consider regarding individual data protection. In particular, the technology of blockchain is difficult to talk about in regard to GDPR, as it’s basically an encrypted and distributed digital ledger. How can blockchain work properly in tandem with the new GDPR regulations?
Dealing with other people, whether in the office or a home environment, can often be troublesome. There is always a case of someone trying to be better than someone else, or trying to take advantage of their naiveté. There are solutions out there that make it easier than ever to help keep your home and business safe. Here are some of the best out there.
The medical field has spawned all kinds of new technology that takes patient care to the next level. Regulations demand that even smaller practices need to make the jump to electronic medical record systems (also known as electronic health records). These EMR/EHR solutions provide an interface that give providers and patients a way to keep themselves connected to each other--a tool to promote a more efficient delivery method for these services. We’ll take a look at these EMR and EHR solutions that are hosted in the cloud, giving your organization more information to make an educated choice on implementing this software.
Late in the summer this past year there were several articles written about how Google would continue to track the location of a person’s smartphone after they had chosen to turn their location settings off. A Princeton researcher corroborated those claims for the Associated Press, traveling through New York and New Jersey with locations services off only to be tracked the entire way. Today, we will discuss this issue, and tell you what you need to know to keep Google from tracking you wherever you go.
Google’s 99 Problems
The perception of Google might be as of a benevolent force in a world full of malevolence to a majority of its users, but over the past few years the problems have been mounting up at the doors of the Googleplex. There has been a laundry list of ongoing legal problems, there has been an employee walkout to protest sexual assault allegations by top executives, and for its continued work as a military contractor. CEO Sundar Pichai appeared before Congress in December to answer lawmakers’ questions about data privacy and company censorship. There has also been a recent dust up with Apple over a violation of Apple App Store policy.
With all these problems on the surface, it would be difficult to assume that Google, or its parent company, Alphabet, Inc. would be raking in dough. That is exactly what has happened. Google took in an astounding $39.3 billion in the fourth quarter of 2018. With every dollar they take in, they take in so much more data. In fact, over the past week, the scrutiny over privacy problems led Google to make the claim that changing their privacy policies--something they will most likely be expected to do--could hurt their company earnings and hinder their ability to create revenue.
So Google Tracks User Data?
Like many of the most utilized services, Google, which owns the Android mobile operating system that powers over 81 percent of all smartphones in the world, tracks data down to an individual level. They contend that they do this to be able to improve their services. The more they know about an individual, the more they know about demographics, and about society as a whole. This gives them the best opportunity to develop, build, and bring to market products and services in line with what people want.
Google has its hands in lots of pies, but its most lucrative, by far, is advertising. In fact, in 2017 Google made $110 billion in profits, $95.4 billion of which came from advertising. In order to be the best they can be at advertising, they need information about consumers (and would-be advertisers).
Google’s tracking tools are numerous.
They have the number one mobile operating system (Android), the number one Internet browser (Chrome), the number one hosted email provider (Gmail), the number one video site (YouTube), the number one search engine (Google Search), and the number one mapping application (Google Maps). This is just a small list of all of Google-owned services as hundreds of millions of people and organizations also use their cloud storage systems, their productivity applications, their virtual assistant, and their news aggregate.
Privacy with Google
With all the services you use tracking every piece of data they can, keeping yourself private with Google around might be harder than you think...or is it? You’d think that you should just be able to go into your Android OS and switch off location settings and they will keep from tracking your whereabouts or your activity. This, of course, is not the case, but there is a relatively simple way to keep your location a secret...even from Google. Throw your phone in a large body of water. If you don’t have a large body of water near you, just run it under the faucet for a couple hours (or long enough for those with that pesky IP68 certification to be proven foolhardy).
We’re just kidding of course. If you want Google to stop tracking you, you will need to find, and toggle off the “Web and App Activity” setting. With this setting turned off, Google will no longer be able to store a snapshot of where you’ve been and won’t have access to browser search metrics either.
This may be annoying to some Google users, as to their understanding once Location History is toggled off, the phone should not be able to track his/her location. Google, defending the miscommunication, stated, “Location History is a Google product that is entirely opt in, and users have the controls to edit, delete, or turn off at any time...we continue to use location to improve the Google experience when they (users) do things like perform a Google search or use Google for driving directions.”
Google’s justifications could make sense, until you consider that a feature called “Web and App Activity” needs to be disengaged in order for Google to stop tracking location, even after you tell the OS to stop tracking location. While the company has a laundry list of valuable services, they continue to try and obtain as much data as they can to drive their ad program’s effectiveness, thus profiting off of consumers’ trust.
Do you think that these major Internet companies reliance on advertising revenue is good for consumers or investors? Who really is profiting? Leave your thoughts in the comments section below.
2018 will be remembered as the year where data privacy was altered forever. From Facebook’s many problems to the launch of the European Union’s General Data Protection Regulation, data privacy has never been a bigger issue than it is today. Let’s take a look at how the GDPR has affected the computing world in 2018-19 and how the past year’s events have created new considerations in individual data privacy.
With more than $16 billion being scammed from more than 16 million people, there is clearly an issue at hand that could use some expert insight. Those who are familiar with Steven Spielberg’s Catch Me If You Can might know that the movie was based on the memoirs of Frank Abagnale, former con man and longtime security consultant of the FBI. With his 45 years of experience with the bureau, Abagnale can safely by considered an expert in cybersecurity and fraud protection.
If you use Facebook, you’re not alone. There are over two billion active users on the platform. Whether you are willing to accept it or not, Facebook is a huge part of a good chunk of the world’s lives. If being a well-connected, with the times, user has always described who you are, then we could have some helpful information oriented towards you in our blog today. We will be discussing your online identity, and who you have told Facebook you are.
In part one of this series we started to go through Facebook privacy failings, but we didn’t really give you any information you can use. For part two, we have decided to take you through some security setting for Facebook.
Facebook has over two billion users, and as a result, it has its fair share of privacy snafus. While they do (finally) make available all of a person’s Facebook information, their strategies to success are important reasons why there are so many privacy concerns throughout the online world.
Making it a priority to know how to take control over your personal information on Facebook is a good place to start. Let’s run through Facebook’s privacy settings, and get you set up with two-factor authentication.
Let’s start from a PC. Head over to facebook.com and log in.
Making Sense of Facebook’s Security and Privacy Options
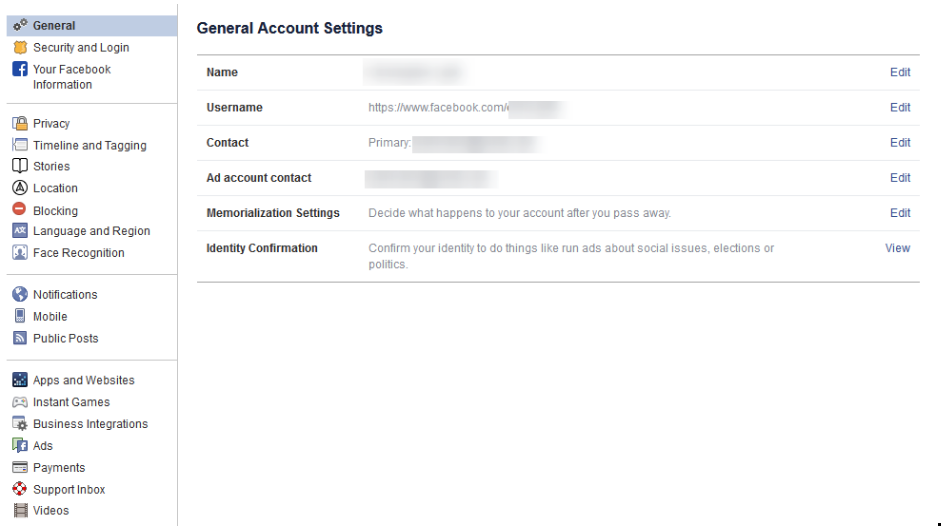
Once you’re logged in to facebook.com, you’ll want to click the little down arrow on the top right of the page. In that menu click on Settings. This can get a little confusing, so if you ever need to start from the beginning know that using the little down arrow can bring you back.
Make Sure the General Account Settings are Right
You will want to verify that you own and control all of the email accounts tied to your Facebook account. If you used an old email address (that you can’t get into), you’ll have a hard time getting back into the account if something were to happen.
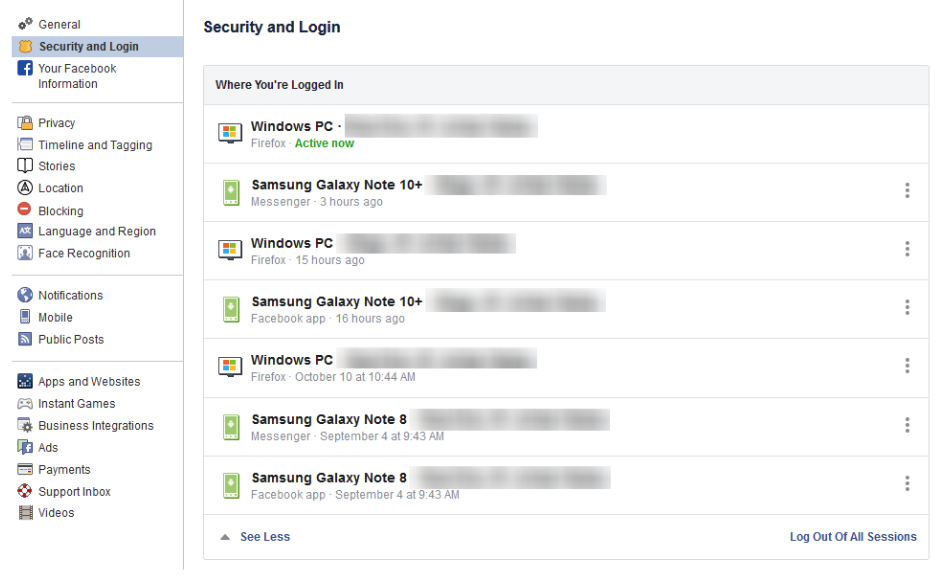
Security and Login - Find Out Where You’ve Logged into Facebook
Click Security and Login on the right.
On this screen, you can see all the devices your Facebook account is currently signed into. You will be confused why there are so many, but think about it: how long have you been using Facebook? For many people it’s not out of line to suggest that they are on their fourth or fifth phone since first using the Facebook app. This means that these devices will show up. You don’t use a Nokia Lumia 920 any longer? Not many people do. Facebook gives you the option to sign out of any of these devices by accessing the three-dot icon next to the device’s name.
It’s a good practice to keep your account logged out on devices you don’t typically use to access Facebook. If you see any suspicious devices among your list of approved devices, you will immediately need to change your password (directions below).
Change Your Password
Changing your password regularly is a good idea, but you definitely don’t want to use the same password over multiple accounts. To do so here, you will want to click on the down arrow on the top right of Facebook, going to Settings, and clicking Security and Login.
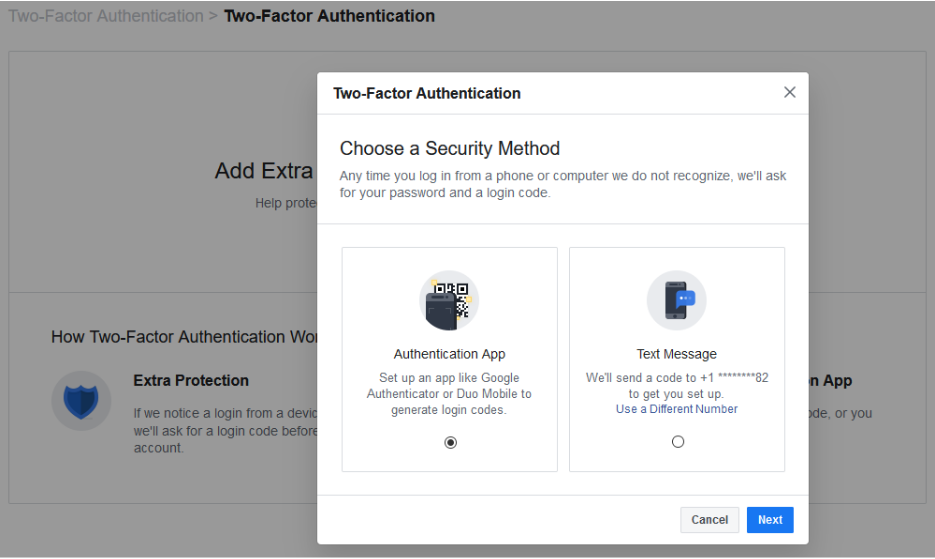
How to Enable Two-Factor Authentication
If you haven't heard of two-factor authentication, it is the practice of setting your account up with an additional layer of security. To get started, select Use two-factor authentication and click edit. Click Get Started.
A screen will pop up that gives you two Security Methods. Before choosing an option, you should understand both.
Option 1 - Authentication App - Clicking on this option will allow you to use a third-party app to authenticate your identity. Popular authentication apps include Google Authenticator, Last Pass Authenticator, or Duo Mobile. Using the authentication app option is more secure than option 2, but it does require you to have access to the mobile device that the authenticator app is installed on.
To set this up, open your authentication app on your mobile device. It makes the most sense to use the authenticator app that you use for other accounts, but if you don’t have one, and you have a Google account, use Google Authenticator.
Then, from Facebook on your computer (see the above screenshot), select Authentication App and click Next.
Facebook will present you with a QR code to scan. In your Authenticator App, add a new account (typically there is a + icon to tap) and scan the QR code. Once scanned, the app will generate a six-digit number to use. Facebook will ask for a Confirmation Code. Type in the six-digit number and you’ll be set.
Option 2 - Text Message - Option number two sends a code via text message to your mobile device. Make sure that you enter the correct number. This method may not be as secure as using an authentication app, but for practical purposes it will do.
Select the Text Message option and click Next, Facebook will text you a code. Type that code into Facebook and voila, you are in.
Depending on the option you choose, Facebook will walk you through the next steps to verify and enable two-factor.
Add a Backup Plan
Once you’ve set up your method, Facebook will provide you with an option to Add a Backup. If you chose to set up two-factor with an Authentication App then Facebook will allow you to set Text Message 2FA as a backup, and vice versa. It’s not a bad idea to set up the other method as well, just in case.
Nowadays, a lot of online accounts offer 2FA, but Facebook also lets you have Recovery Codes (Google also does this, so if you have a Google account or use Gmail, it’s a good idea to get all of this set up over there as well).
Back on the Two-Factor Settings page, under the Add a Backup, there is an option for Recovery Codes.
Click Setup, and Facebook will pop up a window telling you about recovery codes and click Get Codes.
At this time, Facebook will provide you with 10 recovery codes. You can use them in an emergency to get back into your account. These codes are just single-use 2FA codes, so you’ll need to know your password and one of these codes to get back into your account. Since these codes can only be used once, you can request 10 new codes at any time by returning to the Two-Factor Settings page. Keep these codes in a safe place to ensure your account isn’t accessed by anyone else.
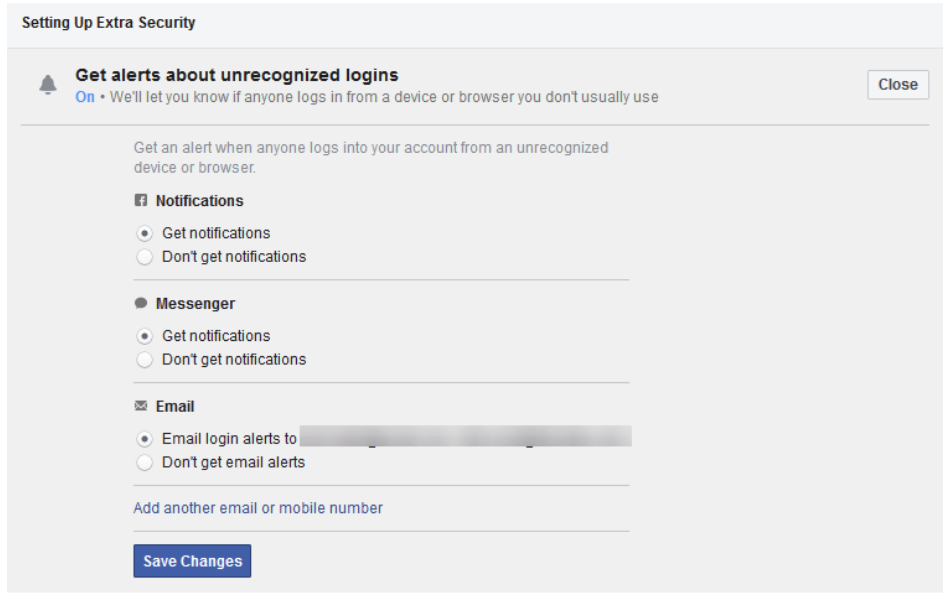
Setting Up Extra Security
If you go back to the Security and Login area of the settings menu, scroll down to Setting Up Extra Security.
This area allows you to set alerts when a new device or browser is used to log into your Facebook. The menu allows you to define additional email addresses. You can also have those notifications sent to you via Facebook Messenger, SMS, or as a Facebook notification.
Below that option, you can choose 3 to 5 Friends to Contact if you get locked out of your Facebook account. If you choose this option, you will want to make sure that you only list people that you trust. If they are like-minded about their own privacy, the better off you will be.
This is admittedly a lot to take in, but setting up two-factor authentication and having control over who can access your Facebook account will go a long way toward securing your Facebook experience. You’ll still be inundated with stupid memes, but at least your personal data will remain secure.
Check back for part three of our Facebook privacy series and leave any thoughts you may have in the comments section below.
Social media - we can’t live with it, but we really can’t seem to live without it. People who frequently read our blog will notice how often we discuss Facebook, one of the biggest players in the social media space. Seeing as privacy is one of the biggest concerns today, we’re wrapping up our short series on Facebook by reviewing the settings you might not have realized were options on your Facebook profile.
Wherever there is money, there are scammers. So it may not be a big surprise that scammers are out in masses trying to get between you and your federally mandated stimulus money. It’s bad enough that we’ve already seen a couple of phishing scams using the COVID-19 pandemic that are designed to help hackers get into accounts they have no business in, now that these scammers know that people are getting cash, the scams are kicked up a notch.
This is not the first time that the U.S. government has distributed checks to everyone, but with online banking being more prevalent now, scammers have a more complete opportunity to steal money. Let’s go through the ways you can ensure that you get your stimulus money:
- Avoid anything that has you sign up for stimulus money - Unless you haven’t filed a tax return in the past two years, you will not have to do much to get your stimulus money. If someone wants you to fill out a form to get your stimulus money, you are definitely being scammed.
- Scammers don’t just act online - Like traditional phishing, you need to be aware everywhere. Whether you get postcards in the mail with a password printed on it or you get messages over social media, you need to know that being asked to take action to gain “access” or to “verify” your payment information is almost assuredly a scam.
- You can’t get your money faster - Some scammers have concocted a scam that “for a small fee” they can get people their stimulus check faster. With tens of millions of people already receiving their check, it's a sign that your money is on its way if you haven’t received it already. No service can help you get your money faster.
- No, you aren’t getting more - What’s better than getting $1,200 tax-free money from your government? Getting more money. Some scammers are actually sending checks for two or three times the amount of the stimulus, the scammer will then apologize for the discrepancy and ask the recipient to reimburse them. The check and their strategy are completely false and should be ignored.
- IRS correspondence - It’s true that some people have had to fill out forms on the IRS website in order to get their checks sent to them or deposited in their bank accounts. Of course, scammers have set up forms that look like it. If the form you filled out isn’t on the IRS’ website, you shouldn’t fill it out.
Knowing what you are up against is the best defense against scammers. If you haven’t yet received your CARES Act stimulus money, you need to go to the official IRS website to find out why (or more likely when) you will receive your stimulus check.
What scams have you been seeing lately? Let us know in the comments section below and return to our blog for more great technology-related information.
While there is no question that security is important to any business, there is often a disconnect between this principle and any actual implementations that it reflects. Unfortunately, this can often leave a business vulnerable. To prevent this outcome, it is important that you follow a few best practices when it comes to fortifying your business against attack.
The inclusion of biometric security systems have been all the rage in a range of organizations, due, in large part, because of the thought that other security platforms aren’t nearly as secure. Unfortunately, the superior security they are expecting may not be able to meet their expectations. Today, we will discuss biometric security, where it fits, and how it can be problematic for the small business.
Today, everything we do on the computer and on our phones creates data. Organizations that are good at utilizing this data, often look to capture everything that they can. This can leave the individual searching for a way to keep his/her data secure. Let’s take a look at some of the best practices used to prioritize individual data privacy.
When a hacker tries to infiltrate your network, they are doing so with a purpose in mind. Usually they are looking for specific information, like account credentials, personal information, or files that can be used to blackmail victims. Regardless, we’ll go over what a hacker can do with the information that they collect from you, and how you can best protect it from them.
The Information Itself
All businesses hold some sensitive information that hackers will do anything it takes to get their hands on. For example, consider what kind of information is collected by the typical business’ human resources department. Naturally, they need all of their employees’ information on record, including birth dates, Social Security numbers, contact information, and other sensitive information. Other departments, like accounting, might need access to financial credentials like credit card numbers or bank account numbers. All of this information is quite valuable for hackers, and they do what they must in order to try and steal it.
Other times, hackers will just try to plant malware - like a keylogger or ransomware, on your company’s network to collect or steal information, like usernames, passwords, and other account credentials. They may then try to use these credentials to hijack accounts or access further information related to your organization, which could result in a major data breach that threatens both the reputation and future of your business.
Sometimes hackers aren’t after information at all, and would rather just cause trouble. Other times, they might plant something like a trojan to create a backdoor for later access. Regardless, hackers are looking to take advantage of your organization’s assets in ways which should cause concern.
The Solution
A comprehensive security solution such as a Unified Threat Management (UTM) solution is your best chance to defend sensitive information from prying eyes. A UTM combines some of the best enterprise-level security solutions on the market into one convenient package especially made for small businesses. A UTM contains a firewall to keep dangerous traffic from entering (or leaving) your network, as well as an antivirus solution that can detect and eliminate threats that have made their way into your infrastructure. Furthermore, preventative measures such as spam blocking and content filtering limit your organization’s exposure to dangerous entities by blocking suspicious messages and inappropriate websites.
If your organization wants to take network security seriously, you need to understand that security shouldn’t be reactive. Instead, you want to take proactive measures to prevent issues. To learn more about what we can do for your business’ network security, reach out to us at (732) 291-5938.
We all know the dangers of doing business with the Internet. Even a small business has sensitive information that could potentially be stolen. While it’s important to take preventative measures to keep threats out of your infrastructure, it’s equally as important to have measures put into place that can detect threats within your infrastructure.
There are numerous threats that can infiltrate your network and lay dormant, waiting to strike at an opportune time. Other threats will lay low on your network and slowly leech data to send to hackers. Some examples are trojans, which will infiltrate a system and create a backdoor that can then be used for future attacks or data leakage. Either way, the important thing is that you need to be able to identify attacks that have managed to thwart your defenses before it’s too late to do anything about it.
Breaches are Inevitable
To understand why threat detection is so important, you need to take on a mindset that you can, and probably will, be hacked sometime in the near future. Even large organizations and enterprises experience hacking attacks, and that’s in spite of enterprise-level security solutions that are designed to prevent breaches from happening in the first place. Think about Sony and the United States Office of Personnel, as well as major health care providers like Excellus BlueCross BlueShield. These companies and organizations didn’t anticipate that they would be hacked, and they paid the price for it.
Thus, you need to expect the worst in order to keep it from happening, and you need to ensure that you’re prepared to handle the worst in this worst-case scenario. This preventative mindset is a common theme in IT security, as it’s much easier to keep problems from happening than it is to react to problems that have happened.
What You Can Do
While preventative measures are effective at keeping most security problems handled, it’s important that you also put a significant effort into detecting threats on your network before any significant damage can be done. CIO recommends what they call a preventative “triad.” This includes protection, detection, and reaction. Not only do you need security solutions, but you also need monitoring tools to detect and eliminate threats.
Working with The Connection, Inc gives you access to enterprise-level security tools that can assist with all three. A Unified Threat Management (UTM) solution includes a firewall, antivirus, spam blocking, and content filtering solution into one convenient package, while a Remote Monitoring and Maintenance (RMM) solution allows for proactive reaction to detected issues on your company’s network. Combined, these solutions can help your organization retain optimal protection from most any threats.
To learn more, reach out to us at (732) 291-5938.